Making sense of our connected world

The Internet in Two Days – an experiment
Undoubtedly, there is no day going by without thoughts or writings concerning the internet – but do we really know how it is actually working? Who, in fact, is well-versed with networks or protocols making our daily use of the Internet possible? Who has ever heard of congestion control or flow control? Probably only a few – provided you did not study informatics before, although both these inventions make the functioning of our today’s internet possible in the first place.
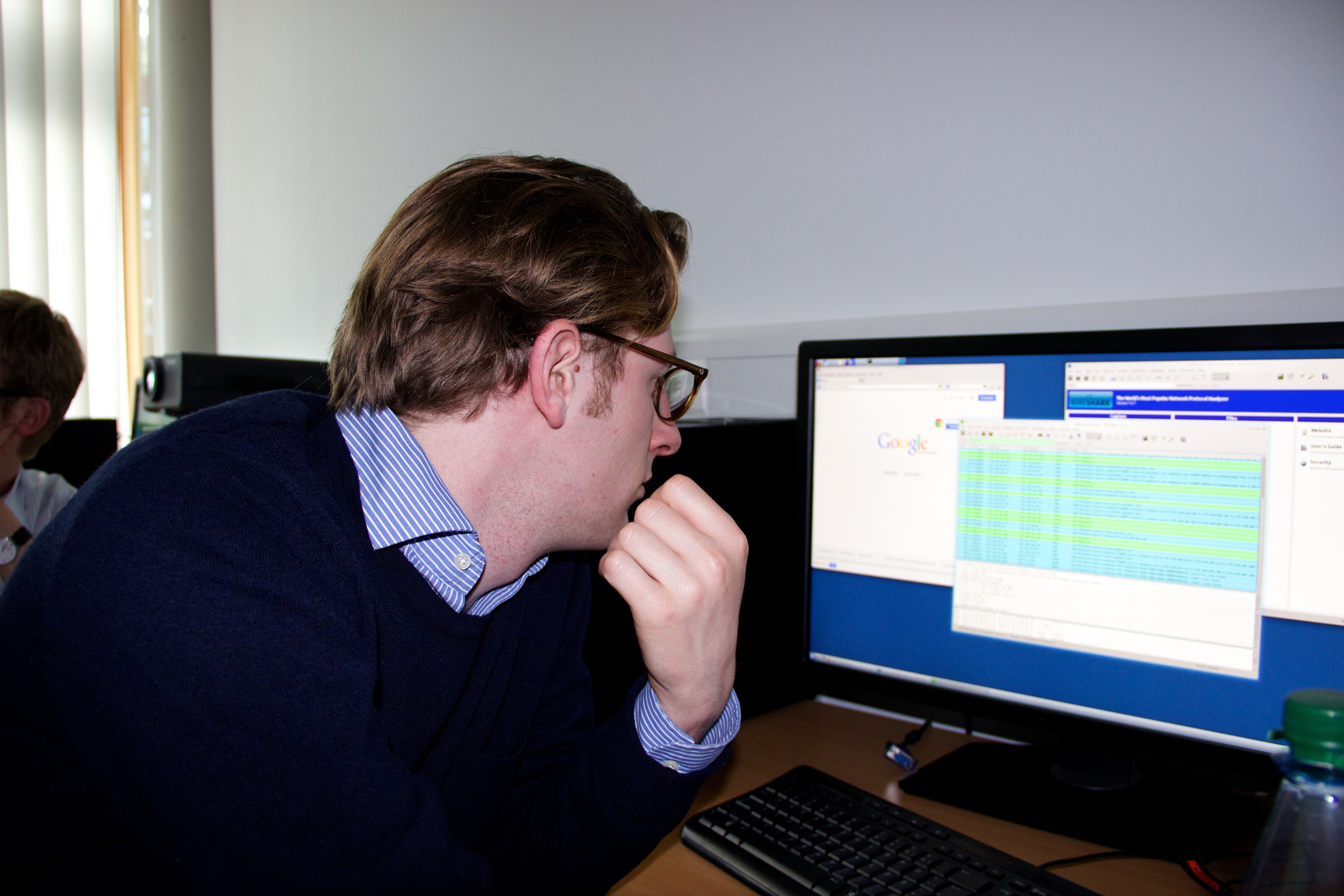
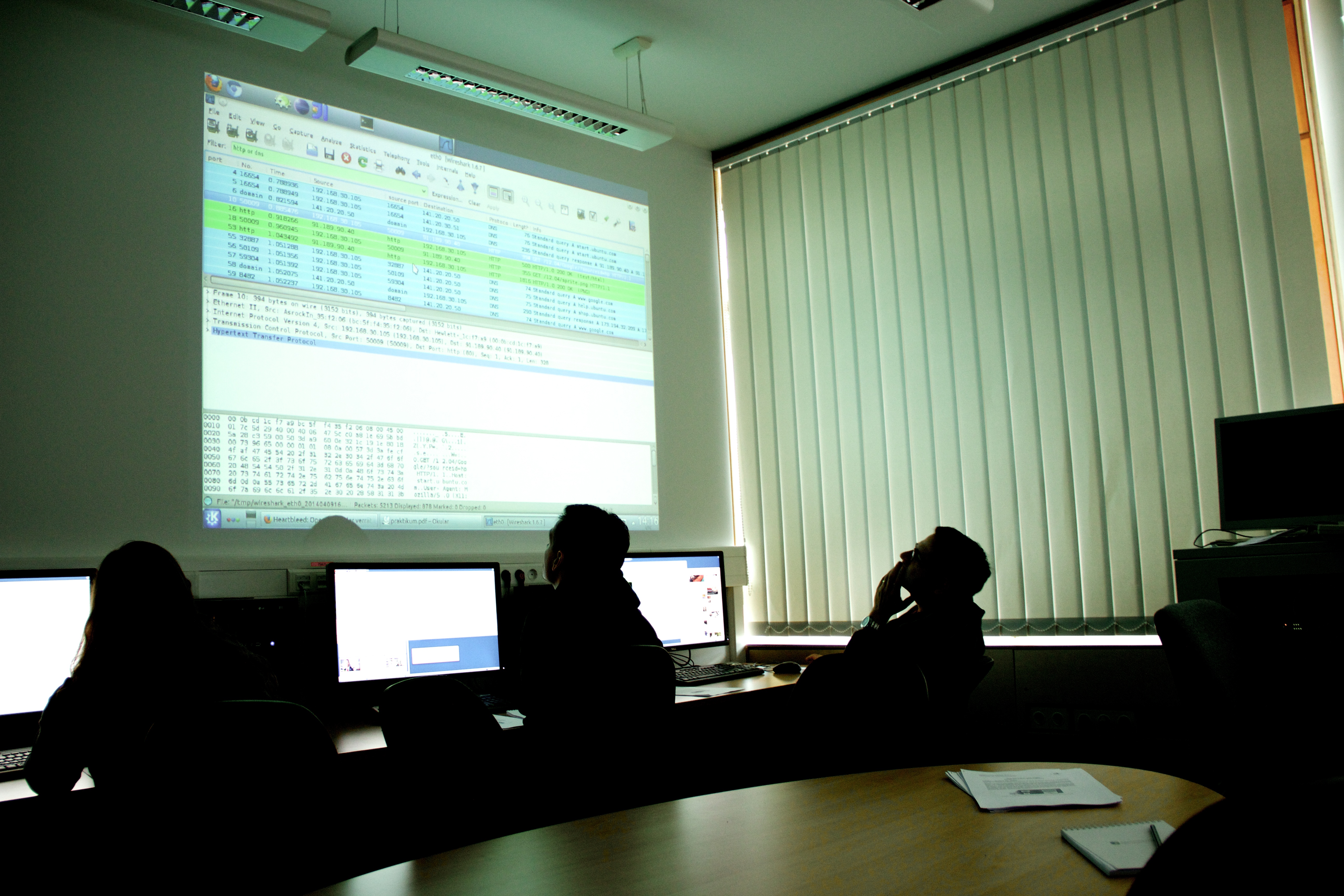
On April 9th and 10th, a group of researchers at HIIG as well as some associate researchers of the Institute had the chance to ask questions one always wanted to know about the internet but were afraid to ask. Prof. Björn Scheuermann from the department of technical informatics of the Humboldt-Universität zu Berlin took two days time for us to elucidate the technical structures of the Internet in a cram course.
The history of the Internet is absolutely no straight success story but rather a story of new challenges. The solutions which were found are not magic but are based on (mostly) quite logical ideas.
On the two-day agenda were various internet layers controlling the worldwide data streams. As we now know, there is the application layer, the transport layer, the network layer, the link layer and the physical layer. What actually happens on the different layers we did examine with examples. We gained insights both into the Simple Mail Transfer Protocol (SMTP) – a rock of protocols in the application layer and up to now regulating data traffic for email applications and Hypertext Transport Protocol (HTTP) which is the transport protocol for websites. We discovered how much time is needed only to understand to some degree the complex functions of the Transport Control Protocol (TCP) being one of the two most common transport protocols in the internet.
The extent of what we learned is hardly to be summarized. The book “Computer Networking: A Top-Down Approach” by James F. Kursoe and Keith W. Ross may be recommended to everybody who has become curious and likes to know more about technical basics of the internet since similar contents are explained there systematically (even if it is not presented as vigorous as by Prof. Scheuermann).
The impressions of the two days were as versatile as the disciplines represented in the workshop:
Out of social scientific point of view, we considered the fact interesting that in our speech about technology technical devices are treated as autonomous actors. It sounds as if routers would make decisions or as computers were able to communicate by themselves which strongly reminds on the Actor Network Theory.
Prof. Ingolf Pernice was especially impressed by the absence of security in the network infrastructure: “There is no security in the internet. Data are being lost or delayed and all in all, it sounds like an experiment and security like we know it from the material world does not exist. And still, the internet is largely accepted.” From the perspective of global constitutionalism, he added: “In terms of global rules, there is no better example as the internet. There was no global legislator and something developed which is applied by half of the world population with a fixed set of rules because it is useful.”
My personal lesson is clear: I assessed how much fun computer science can be (my memories back from school are somehow different). A rough overview of layers and protocols can be achieved quickly, however, close scrutiny may reveal overwhelming complexity of the internet today. The strains to deal with network structures is absolutely worth it if one would like to understand how the internet became what it is today.
This post is part of a weekly series of articles by doctoral candidates of the Alexander von Humboldt Institute for Internet and Society. It does not necessarily represent the view of the Institute itself. For more information about the topics of these articles and associated research projects, please contact presse@hiig.de.
This post represents the view of the author and does not necessarily represent the view of the institute itself. For more information about the topics of these articles and associated research projects, please contact info@hiig.de.

You will receive our latest blog articles once a month in a newsletter.
Featured Topics
AI between climate change and climate protection
How do climate change and artificial intelligence interact? How AI can help in the fight against climate change?
Digital by design, not by default: Resilience in higher education
What does resilience in higher education look like? A comparison of two models from Germany and Portugal shows: there is no single formula.
Algorithms under scrunity: AI observatories as democratic infrastructure
Algorithms have a profound impact on people's lives. This article explores why AI observatories are essential for democratic governance.